ADFS 3.0 is part of Windows Server 2012 R2.
The current version offers some really interesting new features.
In this article I want to provide you a brief overview.
Index
Workplace Join
In times of “bring your own device“, Microsoft now offers a possibility to register and join mobile devices securely. A user can use a protected company resource or application from his or her joined tablet which is not accessible for all external devices.
“Single Sign-On“ is also possible with ADFS 3.0 (user data stays valid for 7 days by default). At the moment, however, only iOS and Windows 8.1 devices are supported.
The Device Registration Service (DRS) is responsible for registration and is part of the ADFS role of Server 2012 R2. Registration takes place either by requesting a certain url or via the Windows 8.1 menu. An unambiguous certificate is created and installed on the device.
This AD-object requires a scheme expansion which can be carried out with the Powershell command Enable-AdfsDeviceRegistration –PrepareActiveDirector.
Enable-AdfsDeviceRegistration
ADFS 3.0 also comes with a new version of ADFS Proxy.
Of course, it also supports registration external of the company network.
Everyone should pay special attention to the service-certificate during installation of the ADFS-role. All devices have to trust this certificate and the following information has to be included:
* Subject Name (CN): adfs1.mydomain.com
* Subject Alternative Name (DNS): adfs1. mydomain.com
* Subject Alternative Name (DNS): enterpriseregistration. mydomain.com
Moreover, the used names have to be registered correctly in the DNS.
Group Managed Service Accounts (GMSA) support
With version 3.0, Microsoft now supports usage of GSMA as service-identities in the ADFS as well.
Group Managed Services Accounts are accounts whose password is generated and renewed automatically by the Active Directory without the administrator’s intervention. This raises security, as passwords are quite long and changed regularly.
Example: Setting up an account
Further information about GMSA: Technet article
OAUTH2 Token Support in ADFS 3.0
ADFS 3.0 is now also capable of generating access-tokens following the OAUTH2 Standard.
These JSON format encoded tokens (JWT JSON Web Token) are particularly compact and built up simply. They are very easy to use in modern web applications.
ADFS Proxy
In former versions of ADFS there was an ADFS-Proxy role. It was mainly installed on servers in the DMZ and forwarded requests from the internet to the internal ADFS.
This function is now a part of the new role “Web Application Proxy” which can only be used together with ADFS and enables the secure sharing of (web) applications in the internet. They also provide you with the possibility to protect “Non claims aware Applications”, meaning applications which cannot analyze token claims (e.g. user properties/ roles) themselves. Analysis of the claims and access to the applications is determined with help of the client and user rules.
Example:
The user is member of a certain group and there is a registered client. User and client are joined.
Of course, Web-Application-Proxy has other features but that would certainly exceed the extent of this article. For further information I recommend this Technet article.
Simplified adaption of the logon website
The logon website can now be adapted to customer wishes even easier and more comprehensively than before: simple Powershell commands for the positioning of logos, company name and help links are provided.
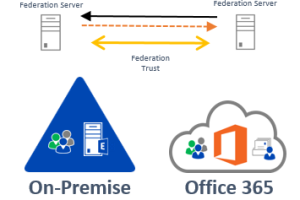
You can read up on scenarios, introduction, functionalities and implementation of SAML and Active Directory Federation Services in the following article: SAML und ADFS 2.0
Please contact us for general questions about the employment of ADFS and possibilities in your company. We would be delighted to assist you.
More: SAML and ADFS
Scenarios, implementation and operation of SAML and Active Directory Federation Services, click the following article:
SAML und ADFS 2.0 (German)
For general questions about the use of ADFS and how to your business can benefit, feel free to contact us.



Leave a Reply
<p>Your email is safe with us.<br/>Information about our <a href="https://activedirectoryfaq.com/contact-us/">data protection policies</a></p>